比赛题目-T23 非对称加密
目录
前言
TIP
骚操作 + 常规加密
思路
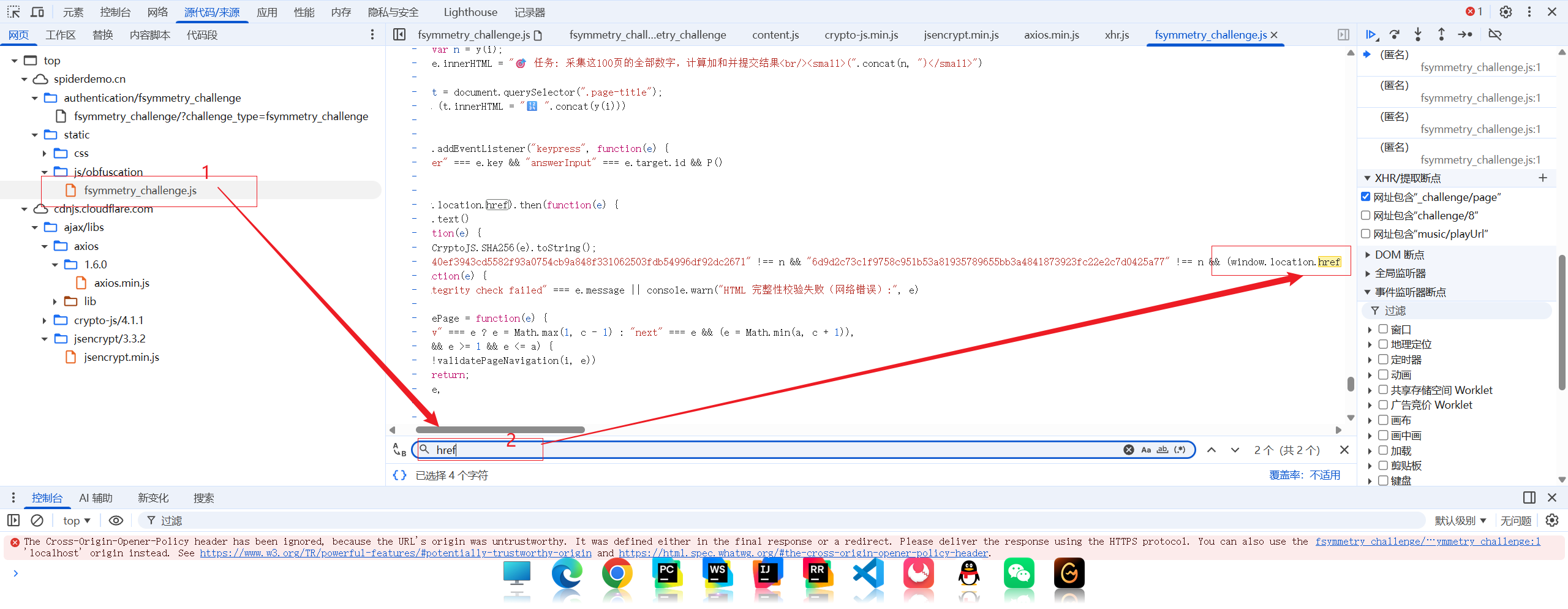
核心问题: 这个题目最难受的在于,一点开题目,立马跳转了一个 https://www.yuanshen.com/#/ 😭😭😭
到这至少让我 知道这个问题和"跳转"相关 ~
也就是 href,这种设计的目的是确保页面内容未被修改(例如,用于反调试、反爬虫或保护特定资源)
怎么办呢?
我的建议是:打断点,script断点 💡 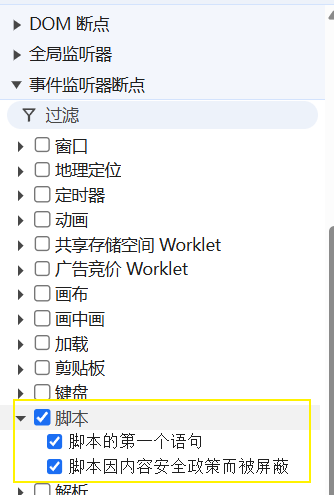
然后,在地址栏,手动输入这一题目的网址,回车 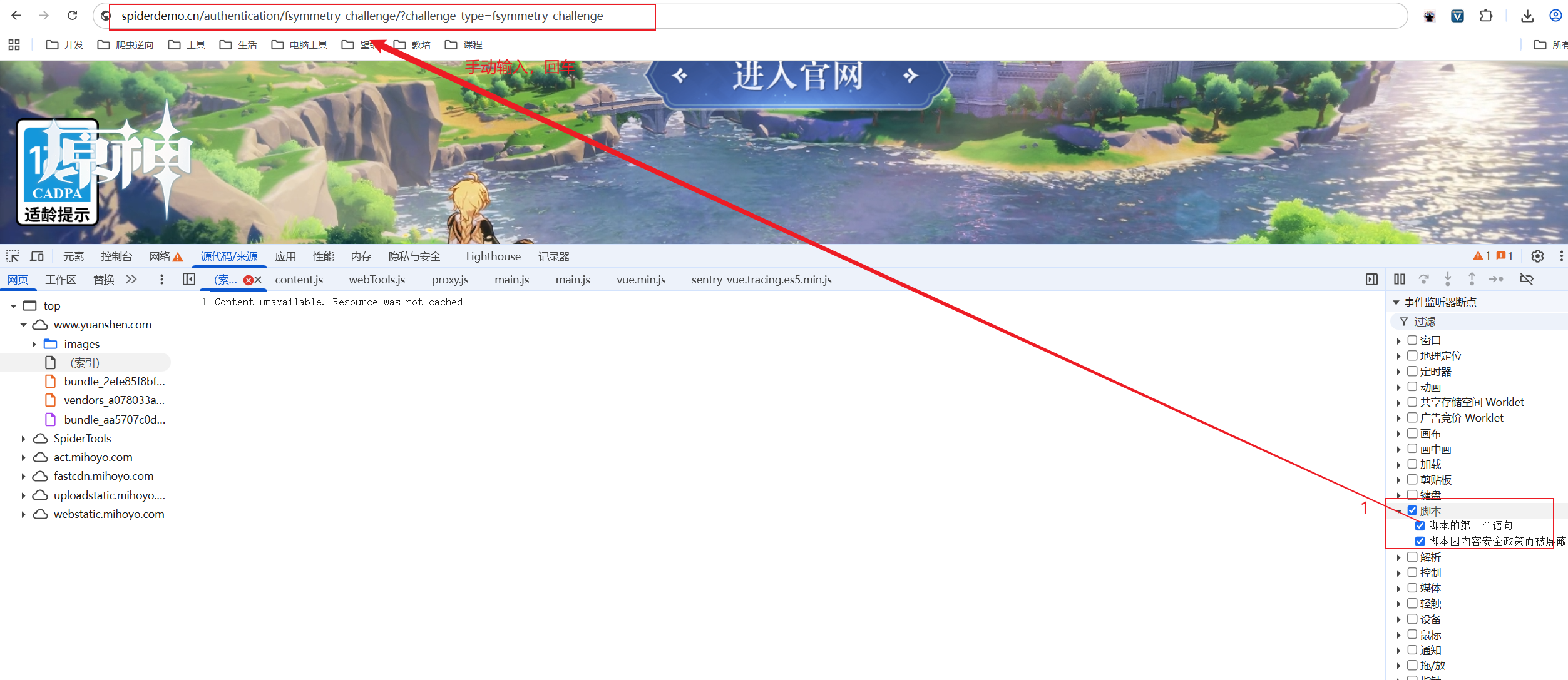
然后 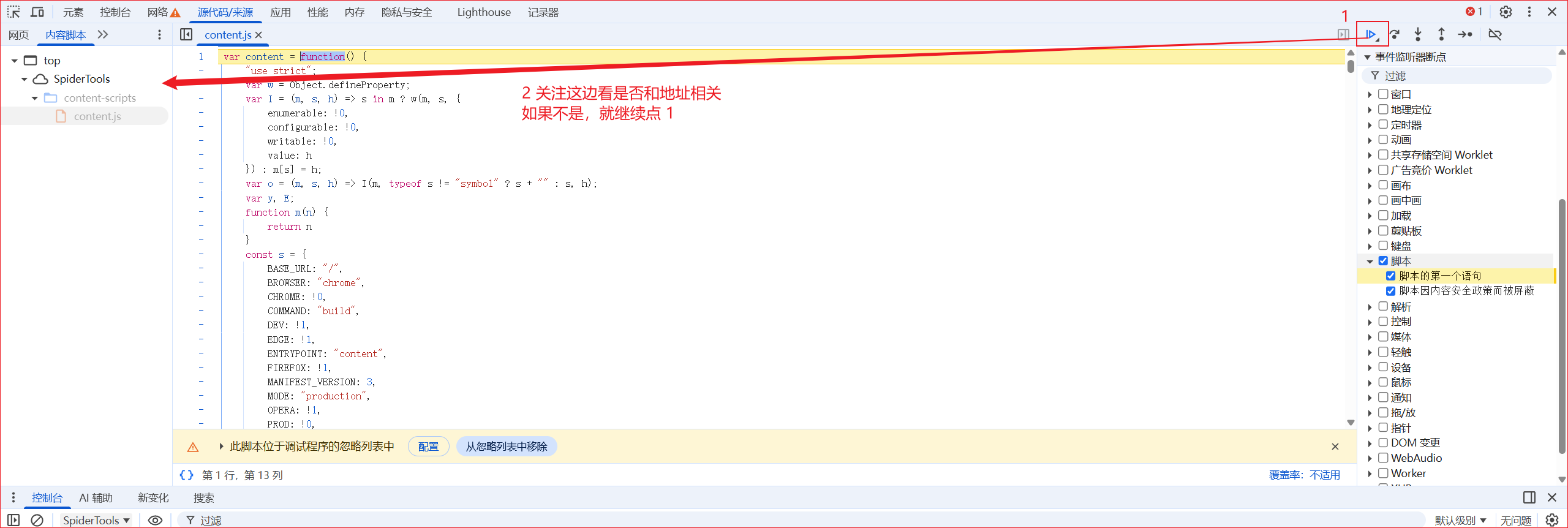
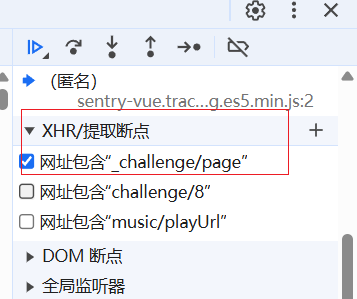
这个时候最好是要多加一个 _challenge/page xhr 断点,拦截request定位参数 💡
js
fetch(window.location.href).then(function (e) {
return e.text()
}).then(function (e) {
var n = CryptoJS.SHA256(e).toString();
"b16486740ef3943cd5582f93a0754cb9a848f331062503fdb54996df92dc2671" !== n && "6d9d2c73c1f9758c951b53a81935789655bb3a4841873923fc22e2c7d0425a77" !== n && (window.location.href = "https://yuanshen.com/")
}).catch(function (e) {
"HTML integrity check failed" === e.message || console.warn("HTML 完整性校验失败(网络错误):", e)
})终于:跳转的原因找到了window.location.href = "https://yuanshen.com/")
这个时候只要把这个过了,咱们就能正常分析了~
两个思路
- hook
- 本地替换,然后删除这段代码,不让跳转!
我这边就用本地替换啦 
然后,在本地,找到window.location.href = "https://yuanshen.com/") 然后删除! 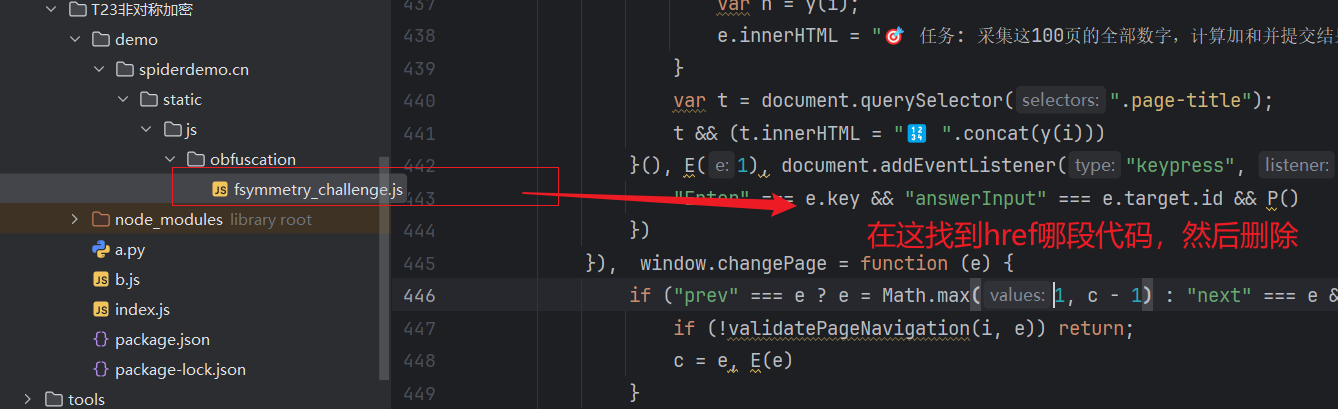
接下来,刷新网页,就发现可以正常看到发包啦 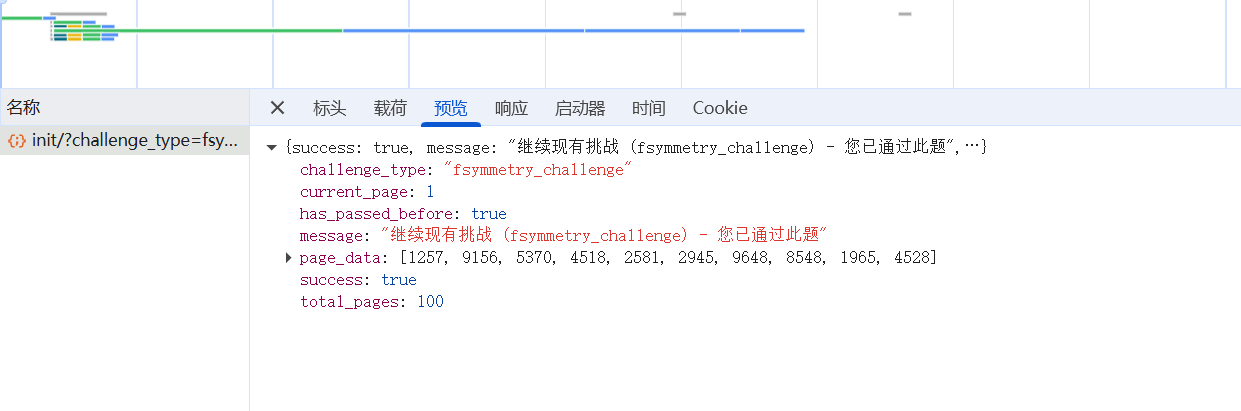
解密
加密参数
看参数
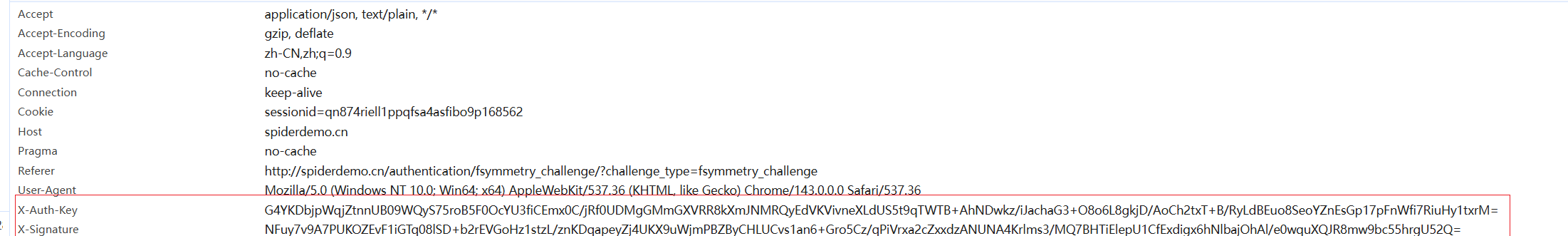
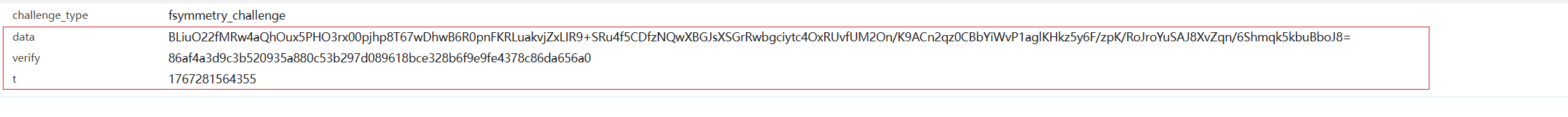
四个加密参数: header: x-auth-key,x-signature param: data,verify,t
搜索参数
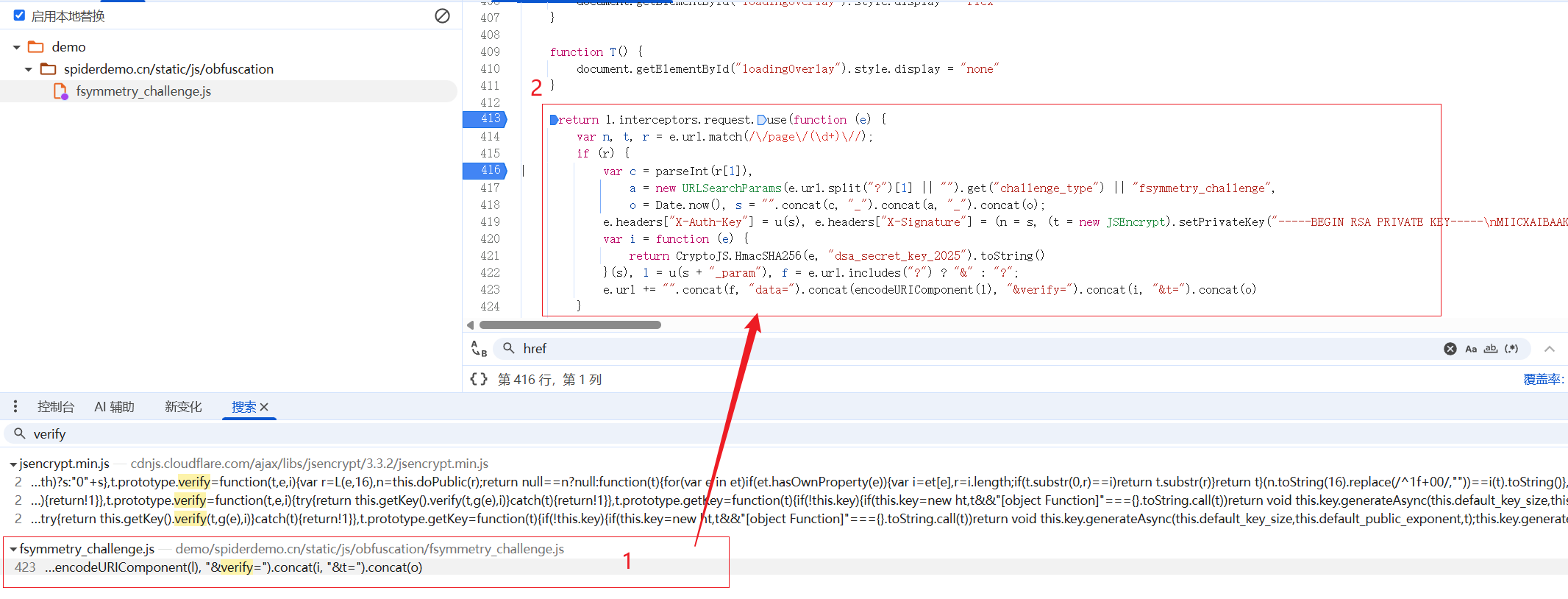
核心加密位置:
js
var n, t, r = e.url.match(/\/page\/(\d+)\//);
if (r) {
var c = parseInt(r[1]),
a = new URLSearchParams(e.url.split("?")[1] || "").get("challenge_type") || "fsymmetry_challenge",
o = Date.now(), s = "".concat(c, "_").concat(a, "_").concat(o);
e.headers["X-Auth-Key"] = u(s), e.headers["X-Signature"] = (n = s, (t = new JSEncrypt).setPrivateKey("-----BEGIN RSA PRIVATE KEY-----\nMIICXAIBAAKBgQC1vKwZUIv7pgpJUXXPpDlD4+VEon3a0ANOrNmqAESrcGfkmYzD\nCo2JeuYezhBGjBNjwVmSct/Y3BBOCRGT2bvtCJGdS12RMvHbFcdbwS/Adh48+rhL\niMNYXLm+7pI3e2k6TlScxKa7EeeZpVtew/Cv5z6ol0llNPp6BdqAlOa8DwIDAQAB\nAoGAS0GaWI9AsFAFEXBgoz/jkMf14DKTgEFEJVexeNLMnNuawhCNuBSOIMCaO2Zk\nWfpWaygdUeYs6M3UGKRruXhf92g/BRmJK5FzR0kWW4qw6WwlYob3TPc3c9MFOjmp\nVtWQ0VSeEPrnBNoQRccKl0dGBnToHGuV+KEuKx8oWZc/JM0CQQDH/cvlx0BKz2zN\n6PM8FidAvc+Wgon8YW81KJgC7iJIrK9FOpctOE3L1pdF7guOQNVGRqN4HCIgLfHE\ncqxWJKJtAkEA6KIkwHe/Q23uWH5GP8DHtVkLVfohTumYkpb0rk05EYQ0dsWSNzWH\nXDH/kD6ayNq+fscnS8g+59onzvfhJ0bq6wJBAKNFkDEHenWY4js481sauvEgBVnb\nOMvSv/emLHQ39cVfNbhPHRzN2rWPe/CbZtO8GmJFSS/FyBZ9a+P1uryZLAECQAaw\nApZ12s25b0yj9KkIhbU05hqGokZ+eKBeLpKELcvPHSL88wMbStTfqxUed5ymjStf\n1kVbcFOB9fsBLTvP0hkCQFCON0l1VjFli+vqfN0lypgIqCf85V6FZFN19creGCCd\n76pX/X2FIBbUSDN1z48SM5I/RKdCkTx7FY+509q2Mek=\n-----END RSA PRIVATE KEY-----"), t.sign(n, CryptoJS.SHA256, "sha256") || "");
var i = function (e) {
return CryptoJS.HmacSHA256(e, "dsa_secret_key_2025").toString()
}(s), l = u(s + "_param"), f = e.url.includes("?") ? "&" : "?";
e.url += "".concat(f, "data=").concat(encodeURIComponent(l), "&verify=").concat(i, "&t=").concat(o)
}扣代码
js
var JSEncrypt = require('jsencrypt')
var CryptoJS = require('crypto-js')
var e = {}
function u(e) {
var n = new JSEncrypt;
return n.setPublicKey("-----BEGIN PUBLIC KEY-----\nMIGfMA0GCSqGSIb3DQEBAQUAA4GNADCBiQKBgQC1vKwZUIv7pgpJUXXPpDlD4+VE\non3a0ANOrNmqAESrcGfkmYzDCo2JeuYezhBGjBNjwVmSct/Y3BBOCRGT2bvtCJGd\nS12RMvHbFcdbwS/Adh48+rhLiMNYXLm+7pI3e2k6TlScxKa7EeeZpVtew/Cv5z6o\nl0llNPp6BdqAlOa8DwIDAQAB\n-----END PUBLIC KEY-----"),
n.encrypt(e) || ""
}
function getParams(page) {
e.url = `/page/${page}/?challenge_type=fsymmetry_challenge`
var n, t, r = e.url.match(/\/page\/(\d+)\//);
if (r) {
var c = parseInt(r[1])
, a = new URLSearchParams(e.url.split("?")[1] || "").get("challenge_type") || "fsymmetry_challenge"
, o = Date.now()
, s = "".concat(c, "_").concat(a, "_").concat(o);
var X_Auth_Key = u(s),
X_Signature = (n = s,
(t = new JSEncrypt).setPrivateKey("-----BEGIN RSA PRIVATE KEY-----\nMIICXAIBAAKBgQC1vKwZUIv7pgpJUXXPpDlD4+VEon3a0ANOrNmqAESrcGfkmYzD\nCo2JeuYezhBGjBNjwVmSct/Y3BBOCRGT2bvtCJGdS12RMvHbFcdbwS/Adh48+rhL\niMNYXLm+7pI3e2k6TlScxKa7EeeZpVtew/Cv5z6ol0llNPp6BdqAlOa8DwIDAQAB\nAoGAS0GaWI9AsFAFEXBgoz/jkMf14DKTgEFEJVexeNLMnNuawhCNuBSOIMCaO2Zk\nWfpWaygdUeYs6M3UGKRruXhf92g/BRmJK5FzR0kWW4qw6WwlYob3TPc3c9MFOjmp\nVtWQ0VSeEPrnBNoQRccKl0dGBnToHGuV+KEuKx8oWZc/JM0CQQDH/cvlx0BKz2zN\n6PM8FidAvc+Wgon8YW81KJgC7iJIrK9FOpctOE3L1pdF7guOQNVGRqN4HCIgLfHE\ncqxWJKJtAkEA6KIkwHe/Q23uWH5GP8DHtVkLVfohTumYkpb0rk05EYQ0dsWSNzWH\nXDH/kD6ayNq+fscnS8g+59onzvfhJ0bq6wJBAKNFkDEHenWY4js481sauvEgBVnb\nOMvSv/emLHQ39cVfNbhPHRzN2rWPe/CbZtO8GmJFSS/FyBZ9a+P1uryZLAECQAaw\nApZ12s25b0yj9KkIhbU05hqGokZ+eKBeLpKELcvPHSL88wMbStTfqxUed5ymjStf\n1kVbcFOB9fsBLTvP0hkCQFCON0l1VjFli+vqfN0lypgIqCf85V6FZFN19creGCCd\n76pX/X2FIBbUSDN1z48SM5I/RKdCkTx7FY+509q2Mek=\n-----END RSA PRIVATE KEY-----"),
t.sign(n, CryptoJS.SHA256, "sha256") || "");
var i = function (e) {
return CryptoJS.HmacSHA256(e, "dsa_secret_key_2025").toString()
}(s)
, l = u(s + "_param")
, f = e.url.includes("?") ? "&" : "?";
e.url += "".concat(f, "data=").concat(encodeURIComponent(l), "&verify=").concat(i, "&t=").concat(o)
}
var pm = {
X_Auth_Key,
X_Signature,
data: l,
verify: i,
t: o
}
return pm
}
//
console.log(getParams(5))请求脚本
py
for page in range(1, 101):
data = {
'page': f'{page}'
}
print(f"第{page}页")
# 调用JS函数生成参数
pm = ctx.call('getParams', page)
print(pm)
headers = {
"Accept": "application/json, text/plain, */*",
"Accept-Language": "zh-CN,zh;q=0.9",
"Connection": "keep-alive",
"Referer": "http://spiderdemo.cn/authentication/symmetry_challenge/?challenge_type=symmetry_challenge",
"User-Agent": "Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/143.0.0.0 Safari/537.36",
"X-Auth-Key": pm['X_Auth_Key'],
"X-Signature": pm['X_Signature']
}
cookies = {
"sessionid": ""
}
url = f"http://spiderdemo.cn/authentication/api/fsymmetry_challenge/page/{page}/"
params = {
"challenge_type": "fsymmetry_challenge",
"data": pm['data'],
"verify": pm['verify'],
"t": pm['t'],
}
# 使用httpx发送请求
response = await client.get(url, headers=headers, cookies=cookies, params=params)
response_data = response.json()
print(response_data)
# 移除exit(),否则只会执行第一页
# exit()
if response_data.get('page_data'):
for item in response_data['page_data']:
count += int(item)
print(f"总计: {count}")完结撒花 🎉🎉🎉
